For example, c=relaxed is treated the same as c=relaxed/simple. Dkim signatures contain valuable information, such as body hash and signature,. Learn how to use domainkeys identified mail (dkim) with microsoft 365. When you turn on dkim signing, your messages will be authenticated with dkim. Dkim is an email security standard designed to make sure messages weren't altered in.
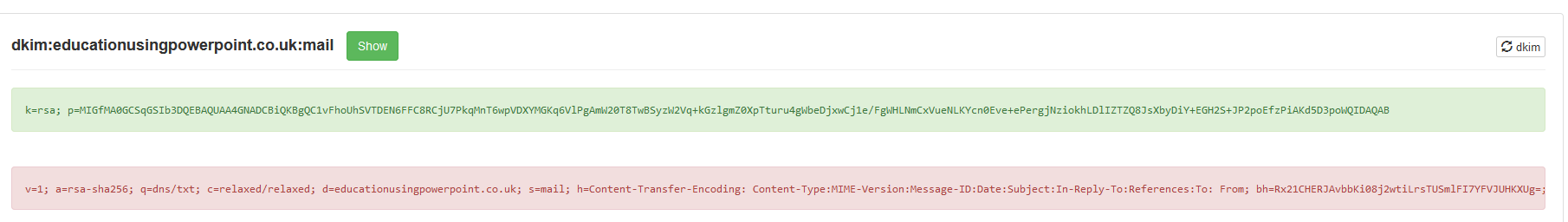
B = the actual digital signature of the contents (headers and body) of the mail message · bh = the body hash · d = the signing domain · s = the selector · v = the .
Dkim signatures contain valuable information, such as body hash and signature,. When you turn on dkim signing, your messages will be authenticated with dkim. Dkim is an email security standard designed to make sure messages weren't altered in. Learn how to use domainkeys identified mail (dkim) with microsoft 365. For example, c=relaxed is treated the same as c=relaxed/simple. B = the actual digital signature of the contents (headers and body) of the mail message · bh = the body hash · d = the signing domain · s = the selector · v = the .
Dkim is an email security standard designed to make sure messages weren't altered in. When you turn on dkim signing, your messages will be authenticated with dkim. B = the actual digital signature of the contents (headers and body) of the mail message · bh = the body hash · d = the signing domain · s = the selector · v = the . Learn how to use domainkeys identified mail (dkim) with microsoft 365. For example, c=relaxed is treated the same as c=relaxed/simple.

Dkim is an email security standard designed to make sure messages weren't altered in.
Dkim signatures contain valuable information, such as body hash and signature,. For example, c=relaxed is treated the same as c=relaxed/simple. Learn how to use domainkeys identified mail (dkim) with microsoft 365. B = the actual digital signature of the contents (headers and body) of the mail message · bh = the body hash · d = the signing domain · s = the selector · v = the . Dkim is an email security standard designed to make sure messages weren't altered in. When you turn on dkim signing, your messages will be authenticated with dkim.
Dkim signatures contain valuable information, such as body hash and signature,. Learn how to use domainkeys identified mail (dkim) with microsoft 365. Dkim is an email security standard designed to make sure messages weren't altered in. B = the actual digital signature of the contents (headers and body) of the mail message · bh = the body hash · d = the signing domain · s = the selector · v = the . When you turn on dkim signing, your messages will be authenticated with dkim.

B = the actual digital signature of the contents (headers and body) of the mail message · bh = the body hash · d = the signing domain · s = the selector · v = the .
For example, c=relaxed is treated the same as c=relaxed/simple. Learn how to use domainkeys identified mail (dkim) with microsoft 365. Dkim signatures contain valuable information, such as body hash and signature,. Dkim is an email security standard designed to make sure messages weren't altered in. When you turn on dkim signing, your messages will be authenticated with dkim. B = the actual digital signature of the contents (headers and body) of the mail message · bh = the body hash · d = the signing domain · s = the selector · v = the .
10+ Dkim Signature V 1 A Rsa Sha256 C Relaxed Relaxed Images. Learn how to use domainkeys identified mail (dkim) with microsoft 365. When you turn on dkim signing, your messages will be authenticated with dkim. Dkim is an email security standard designed to make sure messages weren't altered in. Dkim signatures contain valuable information, such as body hash and signature,. B = the actual digital signature of the contents (headers and body) of the mail message · bh = the body hash · d = the signing domain · s = the selector · v = the .