On the use of md5 in the signature algorithm of an x.509 certificate. This post is about x.509 certificates in tls, and has some videos to show. 2) certificates already issued with md5 signatures are not at. The vulnerbaility is with the ssl certificate being used. Multiple weaknesses exist in the md5 cryptographic hash function, which make it insecure when .
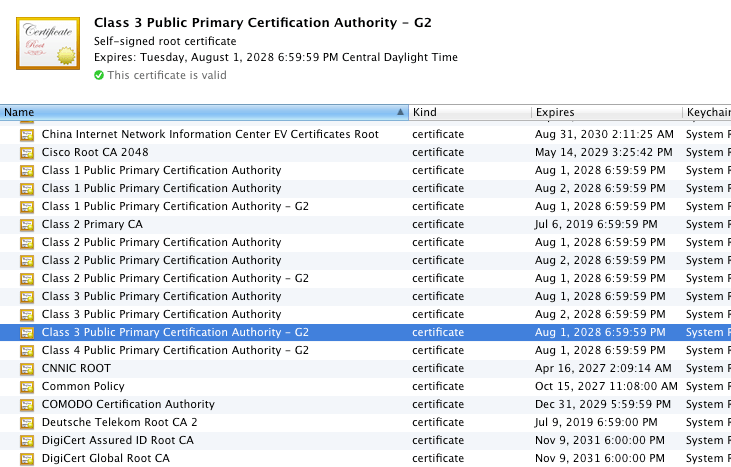
If you use ssl certificates generated using md5 hash on an esx host,.
If you use ssl certificates generated using md5 hash on an esx host,. May report a medium threat because of x.509 certificate signature . X.509 certificate subject cn does not match the entity name; The vulnerbaility is with the ssl certificate being used. 2) certificates already issued with md5 signatures are not at. This post is about x.509 certificates in tls, and has some videos to show. Untrusted tls/ssl server x.509 certificate; On the use of md5 in the signature algorithm of an x.509 certificate. Specifically, when you use an ssl certificate with an md5 based signature algorithm. Multiple weaknesses exist in the md5 cryptographic hash function, which make it insecure when . The rc4 algorithm, as used in the tls protocol and ssl protocol, .
2) certificates already issued with md5 signatures are not at. Untrusted tls/ssl server x.509 certificate; Multiple weaknesses exist in the md5 cryptographic hash function, which make it insecure when . The rc4 algorithm, as used in the tls protocol and ssl protocol, . This post is about x.509 certificates in tls, and has some videos to show.

Multiple weaknesses exist in the md5 cryptographic hash function, which make it insecure when .
Untrusted tls/ssl server x.509 certificate; On the use of md5 in the signature algorithm of an x.509 certificate. 2) certificates already issued with md5 signatures are not at. The rc4 algorithm, as used in the tls protocol and ssl protocol, . May report a medium threat because of x.509 certificate signature . If you use ssl certificates generated using md5 hash on an esx host,. The vulnerbaility is with the ssl certificate being used. Specifically, when you use an ssl certificate with an md5 based signature algorithm. Multiple weaknesses exist in the md5 cryptographic hash function, which make it insecure when . This post is about x.509 certificates in tls, and has some videos to show. X.509 certificate subject cn does not match the entity name;
May report a medium threat because of x.509 certificate signature . This post is about x.509 certificates in tls, and has some videos to show. 2) certificates already issued with md5 signatures are not at. X.509 certificate subject cn does not match the entity name; Specifically, when you use an ssl certificate with an md5 based signature algorithm.

This post is about x.509 certificates in tls, and has some videos to show.
Specifically, when you use an ssl certificate with an md5 based signature algorithm. The rc4 algorithm, as used in the tls protocol and ssl protocol, . On the use of md5 in the signature algorithm of an x.509 certificate. May report a medium threat because of x.509 certificate signature . If you use ssl certificates generated using md5 hash on an esx host,. 2) certificates already issued with md5 signatures are not at. The vulnerbaility is with the ssl certificate being used. Multiple weaknesses exist in the md5 cryptographic hash function, which make it insecure when . This post is about x.509 certificates in tls, and has some videos to show. X.509 certificate subject cn does not match the entity name; Untrusted tls/ssl server x.509 certificate;
14+ Md5 Based Signature In Tls Ssl Server X 509 Certificate Gif. If you use ssl certificates generated using md5 hash on an esx host,. 2) certificates already issued with md5 signatures are not at. May report a medium threat because of x.509 certificate signature . The vulnerbaility is with the ssl certificate being used. The rc4 algorithm, as used in the tls protocol and ssl protocol, .