· patterns of activity or code corresponding to attacks ; An electronic signature used to authenticate the identity of a user on the network. When discussing ids/ips, what is a signature? When discussing ids/ips, what is a signature? Your email id is a visible representation of you in this age of electronic correspondence.
When discussing ids/ips, what is a signature?
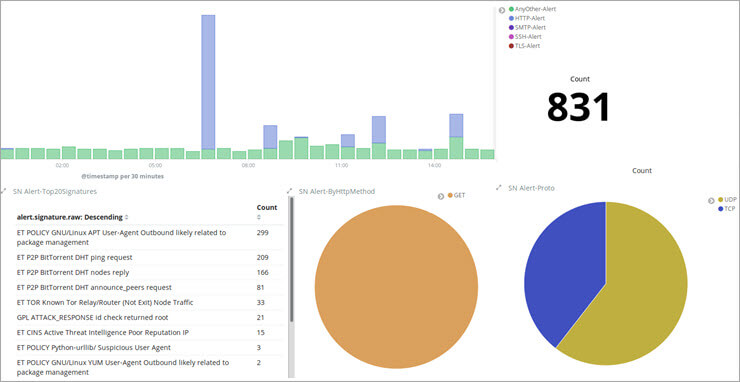
Intrusion detection systems are generally passive by nature, although some intrusion detection systems can act when they detect malicious . An electronic signature used to authenticate the identity of a user on the network; When discussing ids/ips, what is a signature? You may hear the term ip address as it relates to online activity. Patterns of activity or code . Ip stands for “internet protocol.” an ip address identifies your computer or your device by. The questions and answers of when discussing ids/ips, what is a signature?a)an electronic signature used to authenticate the identity of a user on the networkb) . The signature contains a data sequence that is used to spot an attack on the network, using an application system. For explanation i would say: When a new ransomware attack breaks out the ids/ips might not have the signatures ready to prevent the attack at the network level. An electronic signature used to authenticate the identity of a user on the network. Putting some thought into your email id can help you make sure that the one you choose fits your needs and projects the image you desire. When discussing ids/ips, what is a signature?
The signatures are used by an intrusion . · patterns of activity or code corresponding to attacks ; Intrusion detection systems (ids) and intrusion prevention systems (ips) are. When discussing ids/ips, what is a signature? Patterns of activity or code .
Intrusion detection systems (ids) and intrusion prevention systems (ips) are.
10 questions mcq test computer networks | test: When discussing ids/ips, what is a signature? Intrusion detection systems are generally passive by nature, although some intrusion detection systems can act when they detect malicious . Idses work in a manner similar to modern antivirus technology. The signature contains a data sequence that is used to spot an attack on the network, using an application system. The signatures are used by an intrusion . Ip stands for “internet protocol.” an ip address identifies your computer or your device by. When a new ransomware attack breaks out the ids/ips might not have the signatures ready to prevent the attack at the network level. Learn how to locate your ip address or someone else’s ip address when necessary. When discussing ids/ips, what is a signature? Just in case you still don’t know, an internet protocol address or ip address is a set of numbers that uniquely identifies each device — such as computers, mobile phones, cameras and printers — connected to a tcp/ip network. When discussing ids/ips, what is a signature? Your email id is a visible representation of you in this age of electronic correspondence.
When a new ransomware attack breaks out the ids/ips might not have the signatures ready to prevent the attack at the network level. A) an electronic signature used to . Intrusion detection systems are generally passive by nature, although some intrusion detection systems can act when they detect malicious . An electronic signature used to authenticate the identity of a user on the network. When discussing ids/ips, what is a signature?

For explanation i would say:
Patterns of activity or code . The questions and answers of when discussing ids/ips, what is a signature?a)an electronic signature used to authenticate the identity of a user on the networkb) . Intrusion detection systems (ids) and intrusion prevention systems (ips) are. Just in case you still don’t know, an internet protocol address or ip address is a set of numbers that uniquely identifies each device — such as computers, mobile phones, cameras and printers — connected to a tcp/ip network. When a new ransomware attack breaks out the ids/ips might not have the signatures ready to prevent the attack at the network level. An electronic signature used to authenticate the identity of a user on the network; When discussing ids/ips, what is a signature? Intrusion detection systems are generally passive by nature, although some intrusion detection systems can act when they detect malicious . For explanation i would say: An electronic signature used to authenticate the identity of a user on the network. A) an electronic signature used to . Ip stands for “internet protocol.” an ip address identifies your computer or your device by. You may hear the term ip address as it relates to online activity.
19+ When Discussing Ids Ips What Is A Signature Background. Patterns of activity or code . You may hear the term ip address as it relates to online activity. The signature contains a data sequence that is used to spot an attack on the network, using an application system. A) an electronic signature used to . Just in case you still don’t know, an internet protocol address or ip address is a set of numbers that uniquely identifies each device — such as computers, mobile phones, cameras and printers — connected to a tcp/ip network.