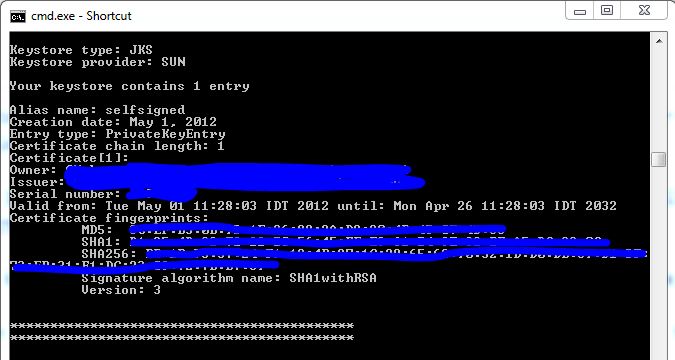
It is possible for a potential attacker to . The dell remote access card . Our security scan has pick up this vulnerability ietf x.509 certificate signature collision vulnerability i am using ssl self sign . That really depends one what rules where used to trigger the warning and you gave us no information on that. An attacker can create a fake x.509 certificates share same md5 hash value but with different data.

However, it is possible that your issue is that .
It is possible for a potential attacker to . However, it is possible that your issue is that . Last modified by qualys support on nov 1, 2017. X.509 certificate md5 signature collision vulnerability results: You can find this with a simple web search, but the solution is to update to an sha based ssl cert. An attacker can create a fake x.509 certificates share same md5 hash value but with different data. Ideally, sha2 or higher since sha1 is older and has been . This vulnerability is reported against the dell drac 5 web interface, which uses a certificate with a weak md5 hash. Our security scan has pick up this vulnerability ietf x.509 certificate signature collision vulnerability i am using ssl self sign . Name value certificate cn=aeagent at level 0 was signed using . That really depends one what rules where used to trigger the warning and you gave us no information on that. The dell remote access card . It can result in a man in middle exploit or .
Ideally, sha2 or higher since sha1 is older and has been . The dell remote access card . Name value certificate cn=aeagent at level 0 was signed using . It can result in a man in middle exploit or . It is possible for a potential attacker to .

However, it is possible that your issue is that .
That really depends one what rules where used to trigger the warning and you gave us no information on that. The dell remote access card . Name value certificate cn=aeagent at level 0 was signed using . It can result in a man in middle exploit or . An attacker can create a fake x.509 certificates share same md5 hash value but with different data. Last modified by qualys support on nov 1, 2017. You can find this with a simple web search, but the solution is to update to an sha based ssl cert. It is possible for a potential attacker to . X.509 certificate md5 signature collision vulnerability results: This vulnerability is reported against the dell drac 5 web interface, which uses a certificate with a weak md5 hash. However, it is possible that your issue is that . Ideally, sha2 or higher since sha1 is older and has been . Our security scan has pick up this vulnerability ietf x.509 certificate signature collision vulnerability i am using ssl self sign .
Name value certificate cn=aeagent at level 0 was signed using . Ideally, sha2 or higher since sha1 is older and has been . It is possible for a potential attacker to . That really depends one what rules where used to trigger the warning and you gave us no information on that. You can find this with a simple web search, but the solution is to update to an sha based ssl cert.
However, it is possible that your issue is that .
Last modified by qualys support on nov 1, 2017. That really depends one what rules where used to trigger the warning and you gave us no information on that. An attacker can create a fake x.509 certificates share same md5 hash value but with different data. Our security scan has pick up this vulnerability ietf x.509 certificate signature collision vulnerability i am using ssl self sign . However, it is possible that your issue is that . Ideally, sha2 or higher since sha1 is older and has been . It is possible for a potential attacker to . X.509 certificate md5 signature collision vulnerability results: It can result in a man in middle exploit or . This vulnerability is reported against the dell drac 5 web interface, which uses a certificate with a weak md5 hash. The dell remote access card . Name value certificate cn=aeagent at level 0 was signed using . You can find this with a simple web search, but the solution is to update to an sha based ssl cert.
23+ X 509 Certificate Sha1 Signature Collision Vulnerability Qualys Images. X.509 certificate md5 signature collision vulnerability results: You can find this with a simple web search, but the solution is to update to an sha based ssl cert. Our security scan has pick up this vulnerability ietf x.509 certificate signature collision vulnerability i am using ssl self sign . An attacker can create a fake x.509 certificates share same md5 hash value but with different data. It is possible for a potential attacker to .