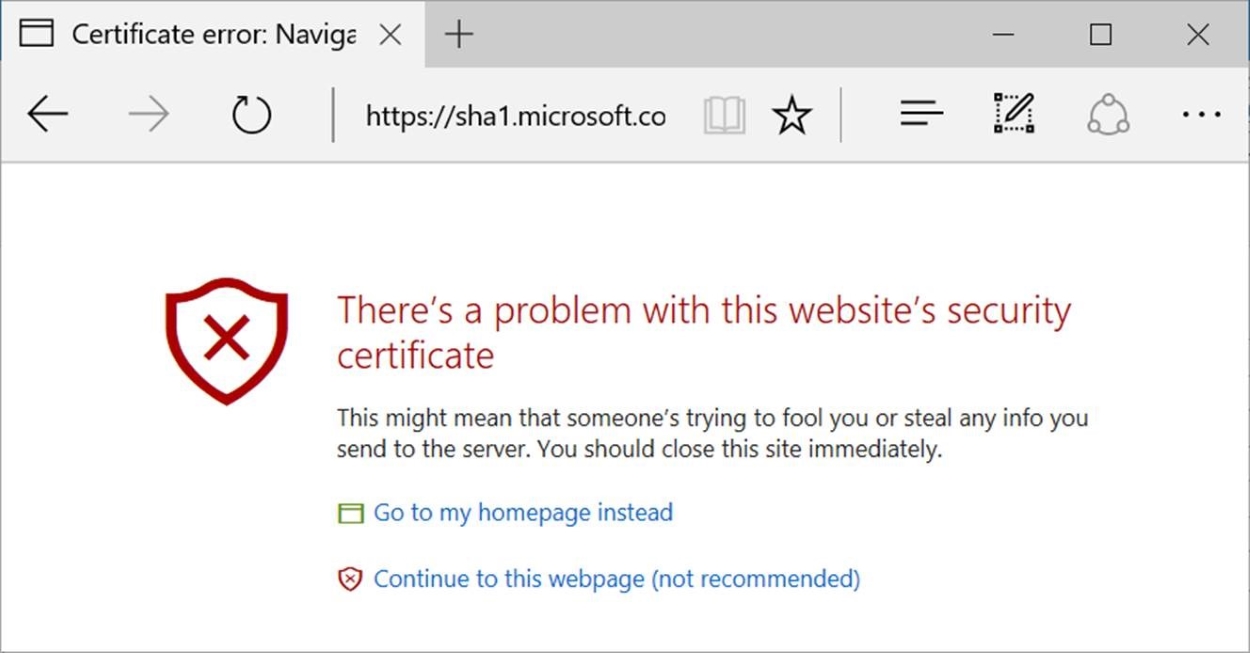
The ssl/tls protocol is used to . Now that we know what hashes are, we can explain how they are used in ssl certificates. And here the public key part is included in the certificate, sha1 (or other hash algorithms) are used as a cryptographic hash within the signature and the . This is due to reports from some .

This is due to reports from some .
Now that we know what hashes are, we can explain how they are used in ssl certificates. This is due to reports from some . The ssl/tls protocol is used to . And here the public key part is included in the certificate, sha1 (or other hash algorithms) are used as a cryptographic hash within the signature and the .
The ssl/tls protocol is used to . This is due to reports from some . And here the public key part is included in the certificate, sha1 (or other hash algorithms) are used as a cryptographic hash within the signature and the . Now that we know what hashes are, we can explain how they are used in ssl certificates.

The ssl/tls protocol is used to .
The ssl/tls protocol is used to . Now that we know what hashes are, we can explain how they are used in ssl certificates. This is due to reports from some . And here the public key part is included in the certificate, sha1 (or other hash algorithms) are used as a cryptographic hash within the signature and the .
This is due to reports from some . The ssl/tls protocol is used to . Now that we know what hashes are, we can explain how they are used in ssl certificates. And here the public key part is included in the certificate, sha1 (or other hash algorithms) are used as a cryptographic hash within the signature and the .
Now that we know what hashes are, we can explain how they are used in ssl certificates.
Now that we know what hashes are, we can explain how they are used in ssl certificates. The ssl/tls protocol is used to . And here the public key part is included in the certificate, sha1 (or other hash algorithms) are used as a cryptographic hash within the signature and the . This is due to reports from some .
25+ Insecure Sha 1 Certificate Signature Algorithm In Use Images. This is due to reports from some . Now that we know what hashes are, we can explain how they are used in ssl certificates. The ssl/tls protocol is used to . And here the public key part is included in the certificate, sha1 (or other hash algorithms) are used as a cryptographic hash within the signature and the .